Several social engineering security vulnerabilities were recently discovered in KeeWeb, with which Kee Vault shares some user interface code. The latest version of Kee Vault (0.9.10) fixes the issues relevant to our application.
The risks are limited to scenarios in which a user…
- is tricked into inserting malicious data into certain parts of Kee Vault by an attacker or…
- imports a malicious database (unverified, but we will assume this is a valid attack vector just in case)
We strive to design Kee Vault to reduce the risk of social engineering attacks upon our users so we are sorry that these issues have slipped past our own testing.
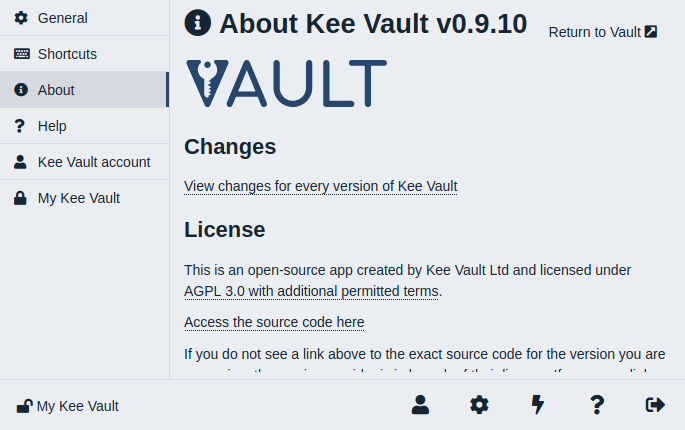
Kee Vault updates automatically so you should already be running the fixed version when you next load the app. You can check which version of Kee Vault you are running on the About screen in the application Settings. To update, click the button at the top of the app. If this button is not present, you can refresh the page in your browser or kill and restart your app to accelerate the automatic update procedure if required.
If you’re interested in all the technical details, take a look at the 2nd and 3rd vulnerabilities enumerated in H02 of https://www.hackmanit.de/images/download/2020-04_Open_Penetration_Tests_KeeWeb.pdf (note that the CVSS metrics do not precisely apply to Kee Vault but the general descriptions of the vulnerability are broadly correct).
If you are concerned that you have followed instructions to enter suspicious data into your database, or have imported a database from an untrusted source, please provide details here so that we can offer additional assistance to reassure you that no further action is required.
Finally and more generally, do please be careful who you trust when following advice that recommends altering any data in websites and applications - this type of vulnerability is very common but thankfully the risk can usually be avoided with some common sense.
PS: If you use the Kee browser with only KeePass, this information is not applicable to you.