This can be used for people who find “high” security level troublesome but still want a stop-gap measure. I’ve seen this feature on KeePassHTTP, but not sure how feasible it is to implement the same for KeePassRPC.
There is a notification every time a new client connects to KeePassRPC for the first time (where you have to type in the short password). Once that client has been approved, there are no further notifications because we’ve already established that you trust the client. If that trust decays over time you might want to adjust the expiry time of the authorisation from within the KeePassRPC options dialog in KeePass. If that’s not quite what you need, what criteria do you suggest we should use to decide what constitutes “attempted access”?
The idea is to minimize the trust required for the browser extension client, so that the database doesn’t get pulled entirely even if the extension is compromised (e.g. a cracker somehow tricked Google/Mozilla to deliver a malicious extension update)
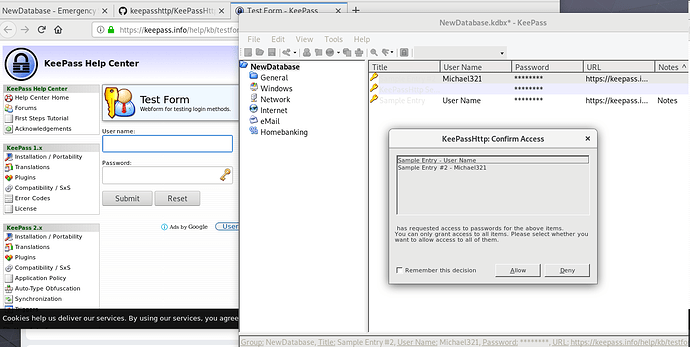
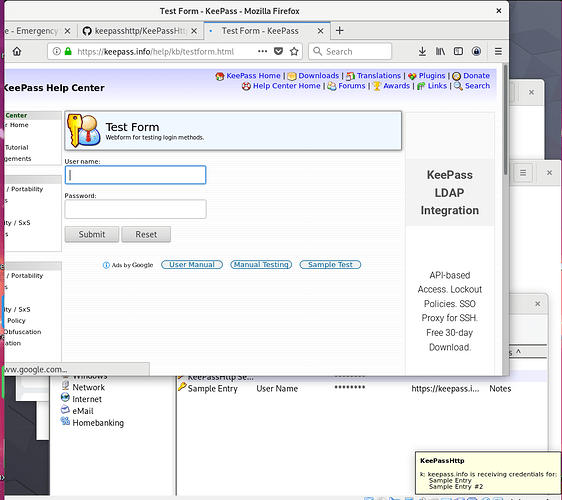
In KeePassHTTP there are 2 modes for this purpose:
- A blocking alert asking confirmation whether a request for some specific records from a client should be allowed.
- A notification noting some specific records are being accessed by a client.